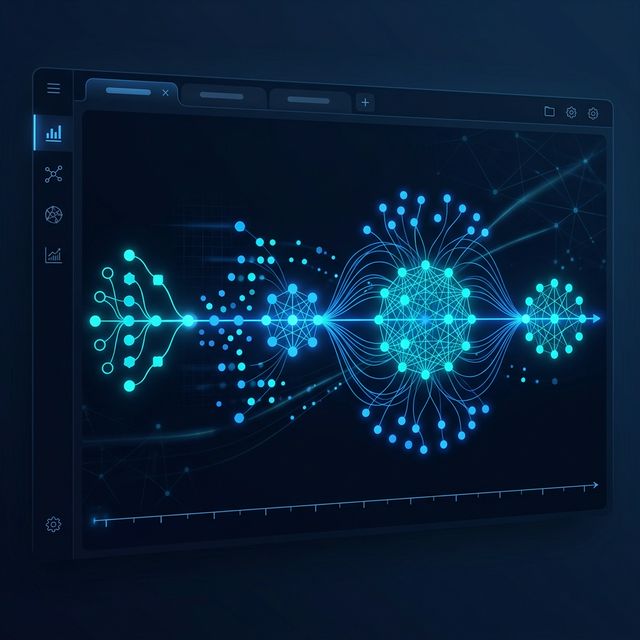
Platform Architecture
A comprehensive overview of how HawkerWatch translates scattered online harassment into structured, review-ready intelligence.
Configurable Thresholds
Not all communication is alike. What constitutes harassment for a private individual may be standard operating noise for a public creator. HawkerWatch allows clients to define strict thresholds based on frequency, platform, and content type.
- Volume triggers (e.g., >5 messages per hour)
- Cross-platform correlation tracking
- Keyword and sentiment flagging
Pattern Detection & Flags
When repeated contact occurs under different burner aliases, isolated reports fail. Our system analyzes behavioral timing, account creation dates, and metadata to cluster suspicious profiles together, flagging when intent escalates from annoyance to targeted obsession.
Warning Workflows
Documentation must sometimes precede action. HawkerWatch provides templates and tracking for formal cease-and-desist communications or platform-specific abuse reports. When notices are issued, the platform logs the transmission as part of the immutable case record.
Notice Transmitted
Log updated accurately with timestamp and delivery receipt protocols.
Evidence Timeline
A disorganized folder of screenshots is easily dismissed. We compile chronologically secure, contextual timelines that show precisely how and when unwanted contact occurred, preserving full context that highlights the trajectory of the behavior.
Escalation & Privacy
When it’s time to involve counsel, our platform exports comprehensive dossiers. Strict access controls ensure that sensitive evidence is only viewable by verified advocates, honoring victim privacy while providing ironclad documentation for professionals.
Zero-Knowledge Architecture
Your data is encrypted. We don't read your logs. We just organize them powerfully.
